(work in progress)
A friend of mine got a new notebook the HP Elitebook 840 G4 with Windows 10. In this blogpost I want to document whats working and what not.
More detailed information about the hardware (lspci). You can also look at the the output of lspci -v
00:00.0 Host bridge: Intel Corporation Device 5904 (rev 02)
00:02.0 VGA compatible controller: Intel Corporation Device 5916 (rev 02)
00:14.0 USB controller: Intel Corporation Sunrise Point-LP USB 3.0 xHCI Controller (rev 21)
00:14.2 Signal processing controller: Intel Corporation Sunrise Point-LP Thermal subsystem (rev 21)
00:15.0 Signal processing controller: Intel Corporation Sunrise Point-LP Serial IO I2C Controller (rev 21)
00:15.1 Signal processing controller: Intel Corporation Sunrise Point-LP Serial IO I2C Controller (rev 21)
00:16.0 Communication controller: Intel Corporation Sunrise Point-LP CSME HECI (rev 21)
00:17.0 SATA controller: Intel Corporation Sunrise Point-LP SATA Controller [AHCI mode] (rev 21)
00:1c.0 PCI bridge: Intel Corporation Device 9d11 (rev f1)
00:1c.3 PCI bridge: Intel Corporation Device 9d13 (rev f1)
00:1d.0 PCI bridge: Intel Corporation Device 9d18 (rev f1)
00:1f.0 ISA bridge: Intel Corporation Device 9d58 (rev 21)
00:1f.2 Memory controller: Intel Corporation Sunrise Point-LP PMC (rev 21)
00:1f.3 Audio device: Intel Corporation Device 9d71 (rev 21)
00:1f.4 SMBus: Intel Corporation Sunrise Point-LP SMBus (rev 21)
00:1f.6 Ethernet controller: Intel Corporation Ethernet Connection (4) I219-V (rev 21)
01:00.0 Unassigned class [ff00]: Realtek Semiconductor Co., Ltd. RTS522A PCI Express Card Reader (rev 01)
02:00.0 Network controller: Intel Corporation Device 24fd (rev 78)
03:00.0 Non-Volatile memory controller: Samsung Electronics Co Ltd Device a804
Installation
I installed Linux Mint 18.1. The only non standard thing i had to do, was to shrink the Windows 10 partition with gnuparted. The installer had no option for that or I did not found it. Other than that, the installation went without a hitch and I was able to start both Windows 10 and Linux mint afterwards.
The kernel which is installed is linux-image-4.4.0-72-generic.
Configuration
As the display of the notebook has 2560×1440 pixel, the user interface was very small and difficult to use with both the mate and cinnamon flavor. Cinnamon has a configuration (Settings-General) where you can scale the interface for high dpi displays as that one. With the option “double” the cinnamon user interface is quite nice and usable.
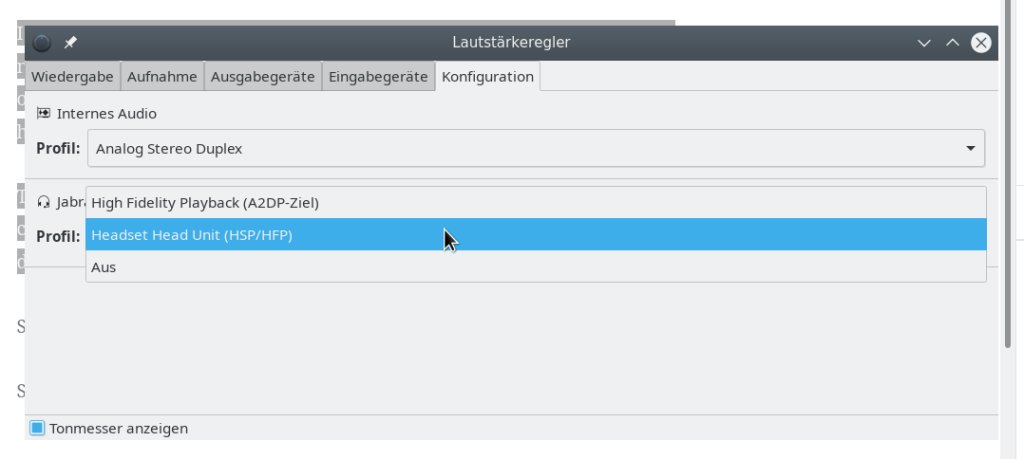
- Sound works out of the box
- Special keys like dimming the display or muting work
Problems
Wifi
As of now, the wifi is not working. There seems to be drivers missing. Output of lshw
*-network UNCLAIMED
description: Network controller
product: Intel Corporation
vendor: Intel Corporation
physical id: 0
bus info: pci@0000:02:00.0
version: 78
width: 64 bits
clock: 33MHz
capabilities: cap_list
configuration: latency=0
resources: memory:d8a00000-d8a01fff
While lspci gives me
Network controller: Intel Corporation Device 24fd (rev 78)
Misc
- The clock is changing in weird ways when booting into windows and linux.
- Standby does not seem to work.